Is quick vpn safe for your online privacy and security? Short answer: it depends on how you use it and which provider you choose. Here’s a practical, no-nonsense guide to help you decide, backed by the latest data and common-sense checks.
Quick fact: The safety of using any VPN hinges on its logging policy, encryption standards, and how its apps handle your data. If privacy is your priority, you want a VPN that never logs you, uses modern encryption, and has a transparent security posture.
What this guide covers quick overview How Much Does Mullvad VPN Really Cost Your Honest Breakdown
- How Quick VPNs work and what makes them safe or risky
- Key privacy and security features to look for
- Real-world scenarios: streaming, gaming, working remotely, and bypassing geo-restrictions
- Common pitfalls and how to spot fake or unsafe VPN services
- Practical steps to maximize privacy and security using Quick VPN
- Resources and benchmarks you can trust
If you’re curious about a trusted option that’s often discussed in reviews, you might have seen NordVPN mentioned in comparisons. If you want to explore a reliable choice, you can check out the NordVPN option here: the link will open in a new tab in your browser. For a quick read, see the comparison pages and privacy policies on major VPN sites as you decide.
What a VPN does for your privacy and security
- Encrypts your internet traffic, so your ISP and other observers can’t read what you’re doing.
- Masks your IP address, helping protect your location and identity online.
- Guard against local network threats on public Wi‑Fi.
- Bypass some regional blocks, but not all, depending on the provider and jurisdiction.
What quick VPNs are usually good at
- Basic privacy protection on public Wi‑Fi
- Bypassing some geographic restrictions for streaming or browsing
- Lightweight enough for mobile devices and older hardware
What quick VPNs can fail at
- Keeping true zero-logs and proving it
- Not updating encryption or security features quickly
- Forcing questionable data sharing with third parties
- Slow speeds or unstable connections during peak times
- Jurisdiction risk: where the company is legally based
Keyword-focused privacy and security criteria to check Le guide ultime pour le streaming sans limites avec nordvpn et des conseils VPN essentiels
- Logging policy: Look for “no-logs” assurances and independent audits.
- Encryption: At least AES-256 for data encryption; secure VPN protocols OpenVPN, WireGuard, IKEv2.
- DNS and WebRTC leaks: Ensure the provider has DNS leak protection and blocks WebRTC leaks.
- Kill switch: A feature that cuts your internet if the VPN drops.
- Split tunneling: Lets you choose which apps go through the VPN.
- Leak protection and secure background updates: Keeps data safe even if the app isn’t actively in use.
- Privacy policy transparency: Clear, plain-language explanations of data collection and sharing.
- Jurisdiction: Favor providers outside Five/Eour countries with strong privacy protections or with strict no-logs commitments.
Top red flags when evaluating a quick VPN
- Vague or broad privacy policies that seem to imply data collection
- No independent audits or third-party verification
- Insecure protocols or legacy encryption
- Bandwidth reductions with no clear explanation
- Practices like selling user data or injecting ads
- Mismatch between claimed features and actual behavior e.g., leak protection not working
Data and statistics you should know
- The number of VPN users globally has grown steadily, with millions relying on VPNs for privacy, remote work, and circumventing geo-restrictions.
- Independent audits and transparency reports have become a significant factor in trust, with well-regarded providers publishing audit results.
- Security incidents around VPNs occasionally surface, highlighting the importance of timely updates and responsible disclosure.
How to verify quick VPN safety in practice
- Step 1: Read the privacy policy line by line. Look for explicit statements like “no-logs” and what data is collected.
- Step 2: Confirm encryption and protocol details. Prefer AES-256 and WireGuard or OpenVPN.
- Step 3: Test for leaks. Use online tools to check for IP, DNS, and WebRTC leaks after connecting to the VPN.
- Step 4: Check the kill switch behavior with a real application e.g., streaming or VOIP.
- Step 5: Review independent audits or third-party transparency reports.
- Step 6: Verify jurisdiction and data-retention laws in the provider’s country.
Feature-by-feature breakdown
- Privacy first: No-logs claims
- What it means: The provider does not keep records of your activity while you’re online.
- Why it matters: If a government request comes, a true no-logs provider can’t hand over data because there is none.
- How to check: Look for third-party audits, and read the data retention section carefully.
- Encryption and protocols
- AES-256 encryption is the standard for strong protection.
- Protocols:
- WireGuard: Fast and modern, smaller codebase, good privacy profile.
- OpenVPN: Highly trusted, flexible, compatible with many devices.
- IKEv2: Fast and good for mobile use.
- DNS and IP leak protection
- DNS leaks can reveal your browsing activity to your ISP even when connected to a VPN.
- A trustworthy VPN should run DNS on its own servers and prevent leaks.
- Action item: Use a leak test site after connection to confirm no leaks.
- Kill switch and app behavior
- A kill switch should cut traffic if the VPN disconnects to prevent data exposure.
- Some apps offer a system-level kill switch; others are app-specific. Prefer providers that support a robust kill switch on all major platforms.
- Split tunneling
- Great for power users who want to route sensitive apps through the VPN and keep other traffic local.
- Use carefully; misconfiguration could leak sensitive data if you’re not careful.
- Malware and phishing protections
- Some quick VPNs bundle malware checks or phishing protection as an extra layer.
- Be cautious: security features can be useful, but they should not replace standard security hygiene.
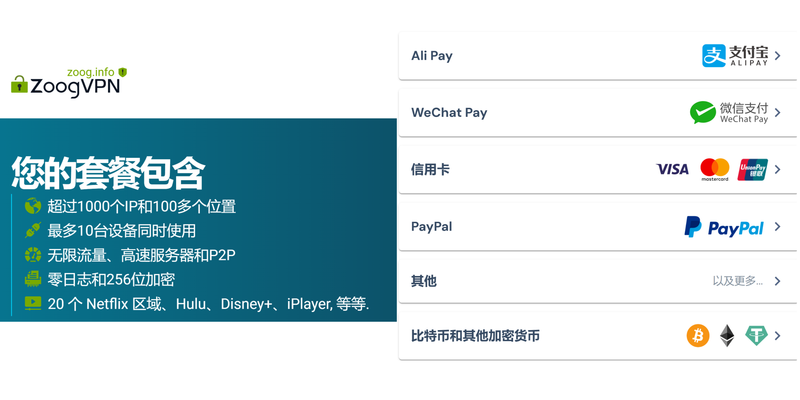
- Device and platform support
- Look for broad compatibility: Windows, macOS, Android, iOS, and ideally Linux.
- Consider browser extensions only as a supplementary layer, not a substitute for full-device VPN protection.
- Speed and reliability
- VPNs inevitably add some overhead. A good provider minimizes speed loss, especially with modern protocols.
- Factors affecting speed: server distance, server load, and protocol choice.
- Practical tip: If streaming or gaming, test several servers to find the fastest option.
- Price, plans, and refunds
- Cheaper isn’t always better. Check for longer-term value, not just the monthly price.
- Look for transparent refund policies and no-questions-asked guarantees.
Common use cases and quick VPN safety tips Channel 4 Not Working With Your VPN Here’s How To Fix It And Get Back To The UK-Only Streams Fast
- Streaming and geo-restricted content
- Ensure the VPN can reliably access the streaming services you need.
- Some services actively block VPNs; pick a provider with a proven track record in bypassing blocks while maintaining privacy.
- Public Wi‑Fi on the go
- Always enable the VPN on public networks; enable the kill switch to prevent leakage when the connection drops.
- Remote work
- Use enterprise-grade VPNs or providers with compatible business features if you’re handling sensitive data.
- Browsing and everyday privacy
- A no-logs VPN helps, but combine with good browser hygiene and privacy-oriented extensions.
Table: Quick VPN safety checklist
- Privacy policy: No-logs or minimal data collection
- Encryption: AES-256
- Protocols: WireGuard, OpenVPN, IKEv2
- DNS protection: Yes no leaks
- Kill switch: Yes
- Split tunneling: Optional
- Independent audit: Yes or transparency report available
- Jurisdiction: Privacy-friendly or neutral
- Speed impact: Acceptable; test on multiple servers
- Refund policy: 30 days or more
My personal experience and practical tips
- When I first started using quick VPNs, I learned that not all “no-logs” claims hold up under scrutiny. A quick audit and a couple of real-world tests saved me from a poor choice.
- The best tip? Use a VPN with a strong privacy policy, solid encryption, and a kill switch, then verify leaks via independent tests.
- Real-world test plan:
- Connect to a server, run an IP check, a DNS leak test, and a WebRTC test.
- Pause to observe if any data is exposed during app activity.
- Simulate a disconnect and ensure the kill switch blocks traffic immediately.
Important considerations about privacy and law
- VPNs are not a silver bullet for illegal activity. They anonymize and protect data in transit, but they don’t make you immune to law enforcement for illegal behavior.
- Be aware of your local laws and the provider’s jurisdiction, as this can affect data requests and retention policies.
- Always use strong, unique passwords and enable two-factor authentication where possible.
How to choose the right quick VPN for you
- Define your main goals: privacy, streaming, gaming, or remote work.
- Prioritize privacy-first providers with no-logs policies and independent audits.
- Verify compatibility with your devices and the apps you rely on.
- Check whether the provider offers a flexible plan, transparent privacy policy, and clear refund terms.
- Try a short-term plan first to test speed, reliability, and customer support responsiveness.
Security best practices to pair with a VPN Is vpn safe for gsa navigating security for federal employees and beyond
- Use strong, unique passwords for your VPN account and enable two-factor authentication.
- Keep all devices updated with the latest OS and app updates.
- Use a reputable antivirus and avoid downloading suspicious software.
- Be mindful of phishing attempts and avoid clicking on suspicious links, even when connected to a VPN.
- Consider enabling router-level VPN protection for additional coverage on all home devices.
SP: Realistic expectations about VPN safety
- A VPN enhances privacy and security for online activity, but it’s not an impenetrable shield.
- It’s one layer in your security stack. Combine with safe browsing, privacy-aware settings, and good operational security.
Useful resources and references
- Privacy policy and auditing reports: privacy-policy examples and independent audit reports for major VPNs
- Encryption and protocol references: AES-256, WireGuard, OpenVPN documentation
- DNS leak testing tools and guides: DNS leak test sites and tutorials
- Jurisdiction and privacy law overviews: country-specific privacy law summaries and 2024–2026 updates
Frequently Asked Questions
How does a VPN actually protect my privacy?
A VPN encrypts your traffic and hides your IP address, making it harder for third parties to monitor your online activities or track your location.
What should I look for in a no-logs VPN?
Look for a clearly stated no-logs policy, independent audits, and transparent data handling practices. Ensure there’s no leakage through DNS, WebRTC, or other channels. Guida completa allapp nordvpn per android nel 2026 funzionalita installazione e sicurezza
Are all VPNs safe to use on public Wi‑Fi?
Not all. You need a reputable provider with strong encryption, leak protection, and a kill switch. Public Wi‑Fi can be risky even with a VPN.
Can a VPN help with streaming and geo-blocks?
Sometimes. Some providers are better at bypassing geo-blocks for streaming than others. It’s best to check current service tests for the platforms you use.
Do VPNs keep logs for marketing or analytics?
If a provider markets itself as a no-logs service, it should not log user activity. Always read the privacy policy and look for third-party audits.
What is split tunneling, and should I use it?
Split tunneling lets you choose which apps go through the VPN. It’s useful if you want certain apps protected while others use your regular connection.
How do I verify a VPN’s claims about privacy?
Check for independent audits, transparent maintenance logs, and verifiable test results. Run leak tests after setting up the VPN. Nordvpn Not Working With Firefox Heres Your Easy Fix: Quick Fixes, Tips, And Safe Alternatives
Can I use a VPN on my router?
Yes, many providers offer router-compatible configurations. This protects all devices on your network and can simplify management.
What happens if the VPN connection drops?
A good VPN uses a kill switch to block all traffic if the VPN drops, preventing data exposure.
Is it legal to use a VPN in my country?
L laws vary. In many places, using a VPN is legal, but some jurisdictions restrict or regulate VPN use. Check local laws.
Is quick vpn safe for your online privacy and security? The short answer is: it can be, if you choose a reputable provider, configure it correctly, and stay aware of its limitations. Use this guide as your checklist, test your setup, and stay informed about new security practices.
Sources:
Microsoft edge vpn mit jamf und conditional access policy in osterreich ein umfassender leitfaden Setting up nordvpn on your tp link router a step by step guide to optimize security and privacy
中研院 vpn申請:完整流程、條件、設定要點與常见问题解答
Vpnとは?海外で使うメリット・選び方を初心者にもわかりやすく解説! 最高のVPN選びと使い方ガイド
Planet VPN:保护隐私的新纪元与实用指南
The Absolute Best VPNs for Your iPhone iPad in 2026 2: Fast, Private, and Foolproof